The federal government should not have warrantless, backdoor access to private communication systems like Twitter.
The federal government unfortunately already has the capability to access everything stored by Big Tech companies, according to recent revelations from Twitter CEO Elon Musk that federal agencies had “full access” to private messages on Twitter.
There has been an ongoing struggle between the federal government and privacy-minded organizations when it comes to allowing back doors into users’ messages and data through sometimes questionable legal avenues. It is unprecedented that certain federal agencies have “full access to everything” in Big Tech systems.
The close partnership between Big Tech and the federal government deteriorates the privacy rights of Americans. This relationship highlights the importance of encryption for protecting Fourth Amendment privacy rights.
The “Twitter Files” revealed that federal agencies had infiltrated Twitter’s decision-making process prior to Musk’s takeover. Musk must clarify not only which federal agencies had “full access” to Twitter direct messages but also what “full access” means. Was the FBI able to read the direct messages of any Twitter user for any reason? How often did they abuse this power, and when did it end?
Elon Musk tweeted on May 10 that Twitter plans to roll out an end-to-end encryption feature for direct messages that will make federal snooping far more difficult. The update would make it so only the individuals receiving direct messages could locally decrypt them on their device, meaning not even Twitter or embedded federal agents could read them.
It is not clear, however, that end-to-end encryption apps are safe from big brother’s illegal inspection.
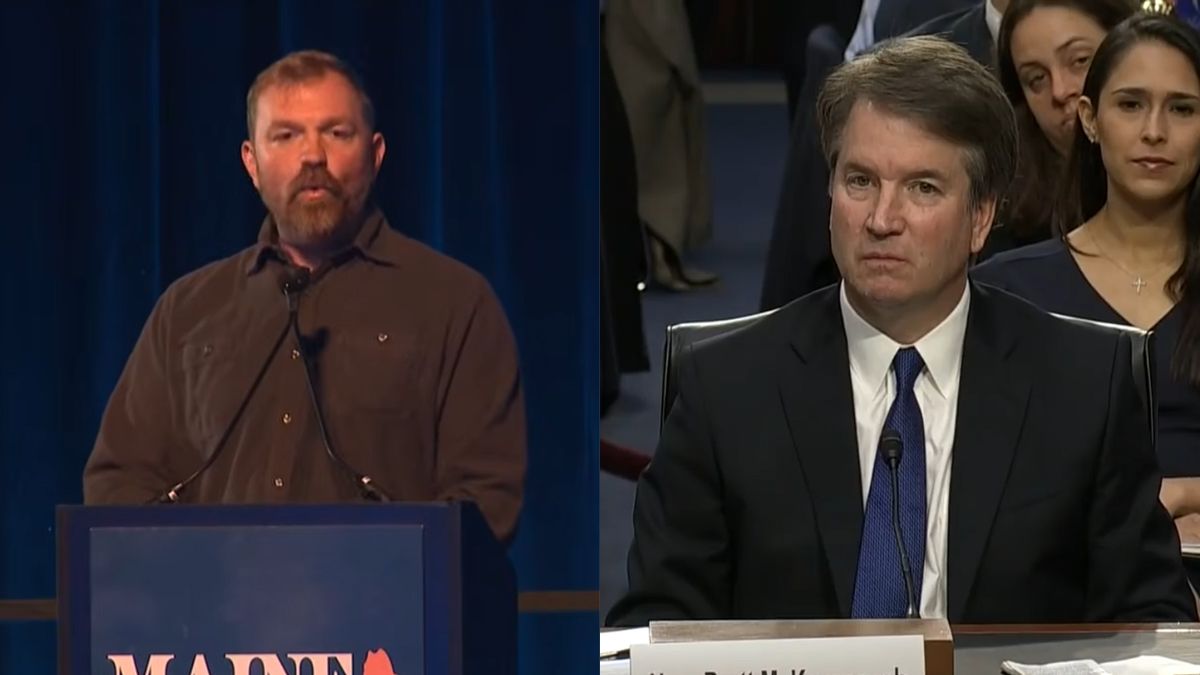
Tucker Carlson, who was interviewing Musk when he made the “full access” comment, spoke on a podcast about a harrowing story involving the encrypted messaging app Signal. According to Carlson, “the NSA broke into [his] Signal account” as he was working to secure an interview with Russian President Vladimir Putin.
The National Security Agency denied it had targeted Carlson specifically but stopped short of denying it had collected his communications. This raises concerns as Signal is encrypted end-to-end, and such an intrusion illustrates that keeping messages private may be impossible.
WhatsApp and iMessage, two very popular messaging apps that are considered secure, have been shown to be less than impervious. While actual message content is safe from view, an FBI document reveals the extent to which the federal government can obtain data about users and their messages through warrants and subpoenas.
Leaked documents have also shown the FBI has attempted to insert back doors into encryption algorithms, which would allow them to decrypt the actual message contents if the compromised algorithms were used. They may be looking to do the same in the future when it comes to quantum-resistant cryptography.
Lawmakers have also considered undermining the strength of encryption algorithms. A Senate bill introduced in 2020 would have made it possible for law enforcement to gain access to encrypted devices by requiring manufacturers and service providers to “assist … with accessing encrypted data.”
Such a law would force technology companies to create ubiquitous back doors for the government. It would also fundamentally undermine encryption algorithms and pave the way for compromise by nefarious actors. There are ways for law enforcement to get around encryption without totally rendering the algorithms defunct for everyone else.
Big Tech has been all too eager to share its users’ information. A New York Times investigation details how often authorities request user data and how infrequently companies like Apple and Microsoft challenge these requests.
If Musk’s revelation is true and Twitter allowed federal agencies to have unfettered access to private user-to-user messages, then it seems Big Tech is enabling this invasive behavior. Is it possible these same federal agencies have similar access to other Big Tech communication services such as Google’s Gmail or Facebook’s Messenger?
There should be no wide-open back door to Big Tech’s systems for the federal government to freely waltz into, and there should be investigations to uncover how pervasive this access may be.
Until then, we should strive to empower users and protect their rights, not law enforcement and Big Tech. Undermining encryption and the privacy it enables would take away a necessary tool in preventing Big Tech and the federal government from abusing their power.