On August 3, 1948, Time magazine’s associate editor Whittaker Chambers testified before the House Un-American Activities Committee that, in the 1930s, he had been “a member of the Communist Party and a paid functionary of that party.” He told the committee he had worked with a network of federal employees to bring about “the Communist infiltration of the American government.” He identified former State Department official Alger Hiss as a member of his spy network.
Hiss, a graduate of Harvard Law School, had clerked for Supreme Court Justice Oliver Wendell Holmes. After his service in the State Department, he became president of the Carnegie Endowment for International Peace, the position he held at the time of Chambers’ testimony. He was Eastern establishment royalty with a distinguished record of public service and an impeccable reputation. The accusation that he had been a Communist set off a media frenzy.
One month later, Hiss sued Chambers for defamation. During civil discovery in that case, Hiss’ lawyers demanded that Chambers produce written proof of his relationship with their client. They were confident that Chambers was lying.
Much to their shock and utter dismay, Chambers produced copies of stolen State Department cables that he claimed Hiss had provided for use by Soviet intelligence. In addition to being a Communist, the civil discovery had produced physical evidence that Hiss had been an espionage agent for the Russians.
This astonishing development resulted in the Justice Department launching a criminal investigation. Because the statute of limitations had expired on any possible espionage charges, the government laid a perjury trap. Before the grand jury Hiss denied under oath that he had passed copies of stolen government documents to Chambers. Consequently, he was indicted, convicted of perjury, and sentenced to five years imprisonment.
This cautionary tale is a prime example of the unexpected consequences of litigation. By pursuing his civil claim for defamation, Hiss sowed the seeds of his own destruction in criminal court. He went to prison because he had failed to realistically assess the dangers inherent in filing his lawsuit.
Another Set of People Underestimate Discovery
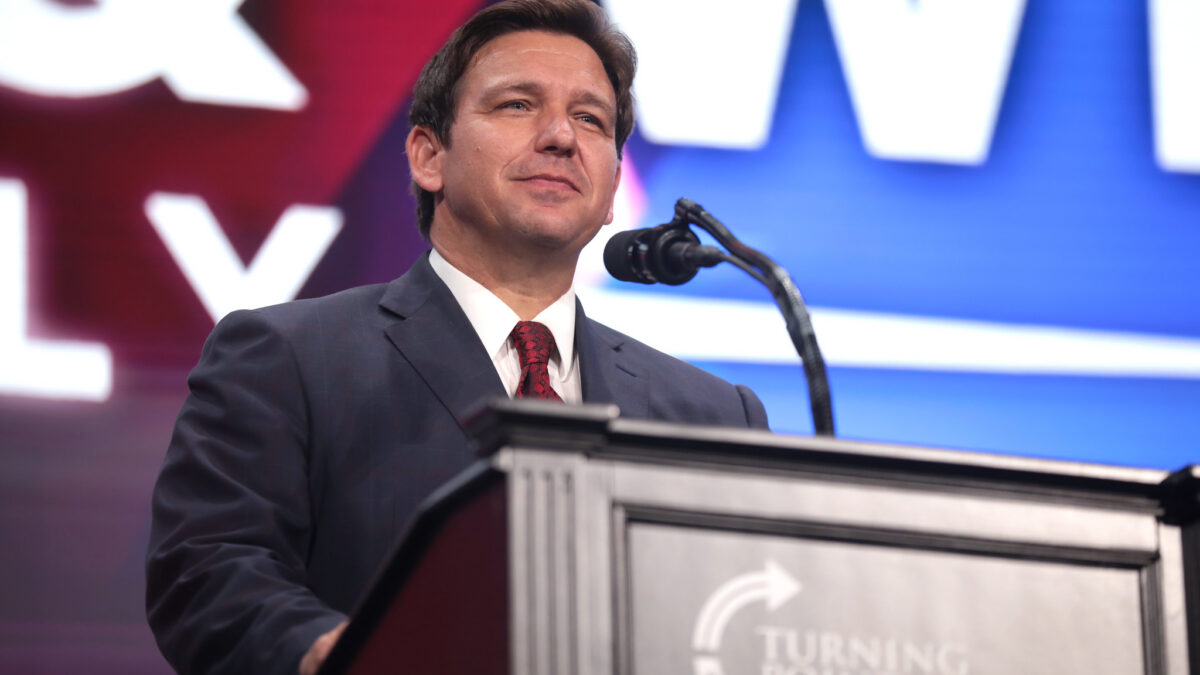
That brings us to the recent lawsuit filed by the Democratic National Committee alleging an illegal conspiracy by President Trump, the 2016 Trump campaign, Republican strategist Roger Stone, Paul Manafort, WikiLeaks, and others with the Russian government to win the 2016 presidential election. Central to the conspiracy was the purported hacking by the Russian government of the DNC’s computers and the dissemination of the hacked emails to harm Hillary Clinton’s candidacy.
The DNC is trying to break new legal ground. Apparently it believes that losing a political campaign is grounds for money damages or something. The legal basis for recovery is murky at best.
But what is clear is that the DNC is following in Hiss’s path. It has hung its case on the alleged Russian hack. Since this is central to its theory of liability, it is going to have to prove by a preponderance of the evidence (the level of proof in civil cases) that the Russians did the hacking and shared the results with the Trump campaign. On the other hand, the defendants are now able to legally test and challenge that claim.
Assuming the case survives a motion to dismiss for failure to state a valid legal claim, the DNC has just opened itself up to civil discovery by the defendants, who can now compel the production of documents and other physical things, and take the depositions of DNC officials, employees, associates, candidates, operatives, and others. In short, the DNC has just invited the defendants to peruse its most deeply held secrets.
The attorneys for defendant Roger Stone have already notified the DNC that it must preserve its files, email server, and other purported evidence of hacking. Their notice states, “One purpose of this letter is to advise the DNC we intend to test the basic underlying claims that ‘Russians’ hacked, stole, and disseminated DNC data, rather than the various other plausible scenarios, including internal theft.”
Based on the available evidence, in challenging the Russian hacking story, Stone’s lawyers appear to be on solid ground. From the very beginning, that narrative has never passed the smell test.
How Russian Hacking Became a Thing
On June 15, 2016, CrowdStrike, a private computer security company the DNC hired, announced it had detected Russian malware on the DNC’s computer server. The next day, a self-described Romanian hacker, Guccifer 2.0, claimed he was a WikiLeaks source and had hacked the DNC’s server. He then posted online DNC computer files that contained metadata that indicated Russian involvement in the hack.
On July 22, 2016, just days before the Democratic National Convention, WikiLeaks published approximately 20,000 DNC emails. Much to the embarrassment of Hillary Clinton, the released files showed the DNC had secretly collaborated with her campaign to promote her candidacy for the Democratic presidential nomination over that of Bernie Sanders. This caused the Clinton campaign serious political damage.
Well after the convention, Jennifer Palmieri, Clinton’s public relations chief, said in a March 2017 Washington Post essay that she worked assiduously during the nominating convention to “get the press to focus on… the prospect that Russia had not only hacked and stolen emails from the DNC, but that it had done so to help Donald Trump and hurt Hillary.”
When the Department of Homeland Security and the FBI learned of the hacking claim, they asked to examine the server. The DNC refused. Why would the purported victim of a crime refuse to cooperate with law enforcement in solving that crime? Is it hiding something? Is it afraid the server’s contents will discredit the Russia-hacking story?
Intel Professionals Investigate These Claims
The answers to those questions began to emerge thanks to an article in the August 8, 2017 issue of The Nation. By no means a pro-Trump publication, The Nation published an exhaustive report about an exacting forensic investigation of the DNC hack by the Veteran Intelligence Professionals for Sanity (VIPS), an organization of former CIA, FBI, National Security Agency, and military intelligence officers, technical experts, and analysts.
As reported by The Nation, VIPS has a well-established record of debunking questionable intelligence assessments that have been slanted to serve political purposes. For example, in the run-up to the U.S. invasion of Iraq, VIPS courageously and correctly challenged the accuracy and veracity of the CIA’s intelligence estimates that Saddam Hussein possessed weapons of mass destruction and posed a threat to the United States. Similarly, VIPS has condemned the use of “enhanced interrogation techniques” on suspected terrorists. In short, VIPS can hardly be described as either a right-wing cabal or as carrying water for the Republican Party.
In its analysis of the purported DNC hack, VIPS brought to bear the impressive talents of more than a dozen experienced, well-credentialed experts, including William Binney, a former NSA technical director and cofounder of the NSA’s Signals Intelligence Automation Research Center; Edward Loomis, former NSA technical director for the Office of Signals Processing; and Skip Folden, a former IBM information technology manager. As the French would say, these are l’hommes serieux.
As set forth in the article, VIPS’ investigative findings were nothing short of stunning. First, VIPS concluded that the DNC data were not hacked by the Russians or anyone else accessing the server over the Internet. Instead, the data were downloaded into a thumb drive or similar portable storage device physically attached to the DNC server.
The time stamps contained in the released computer files’ metadata establish that, at 6:45 p.m. July 5, 2016, 1,976 megabytes (not megabits) of data were downloaded from the DNC’s server. This took 87 seconds, which means the transfer rate was 22.7 megabytes per second, a speed, according to VIPS, that “is much faster than what is physically possible with a hack.” Such a speed is accomplished by directly connecting a portable storage device to the server. Accordingly, VIPS concluded that the DNC data theft was an inside job by someone with physical access to the server.
VIPS also found that, if there had been a hack, the NSA would have a record of it that could quickly be retrieved and produced. But no such evidence has been forthcoming. Can this be because no hack occurred?
Even more remarkable, the experts determined that the files Guccifer 2.0 released were “run, via ordinary cut and paste, through a template that effectively immersed them in what could plausibly be cast as Russian fingerprints.” In other words, the files were deliberately altered to give the false impression that they were hacked by Russian agents.
Thanks to the VIPS experts, the Russia-hacking claim — the lynchpin of the DNC’s lawsuit — appears to have been affirmatively and convincingly undercut.
Did the DNC Use Russia as a Cover?
Moreover, co-defendant Julian Assange has repeatedly denied that Russia “or any state actor” was the source of the stolen DNC data WikiLeaks published. His denials just received confirmation in a recent issue of The New Yorker. It features a lengthy and sympathetic portrayal of British spy Christopher Steele, who gathered the dirt for the DNC-funded anti-Trump dossier that forms the basis for the entire Trump-Russia collusion narrative.
Buried toward the end of the article comes the revelation that, on July 26, 2016, four days after WikiLeaks published the DNC emails, “Steele filed yet another memo” in which “Steele’s sources claimed that the [DNC] digital attack involved agents ‘within the Democratic Party structure itself…’”
All of this raises many questions concerning the DNC’s Russia hacking claim as well as its involvement in spreading the rapidly disintegrating Trump-Russia collusion narrative.
After the DNC denied law enforcement access to its server, the FBI — under James Comey’s leadership — meekly agreed to accept CrowdStrike’s findings as to the server’s contents. This was in lieu of the FBI using legal process (such as a search warrant or forthwith grand jury subpoena) to seize and search the server for Russian malware and evidence of hacking.
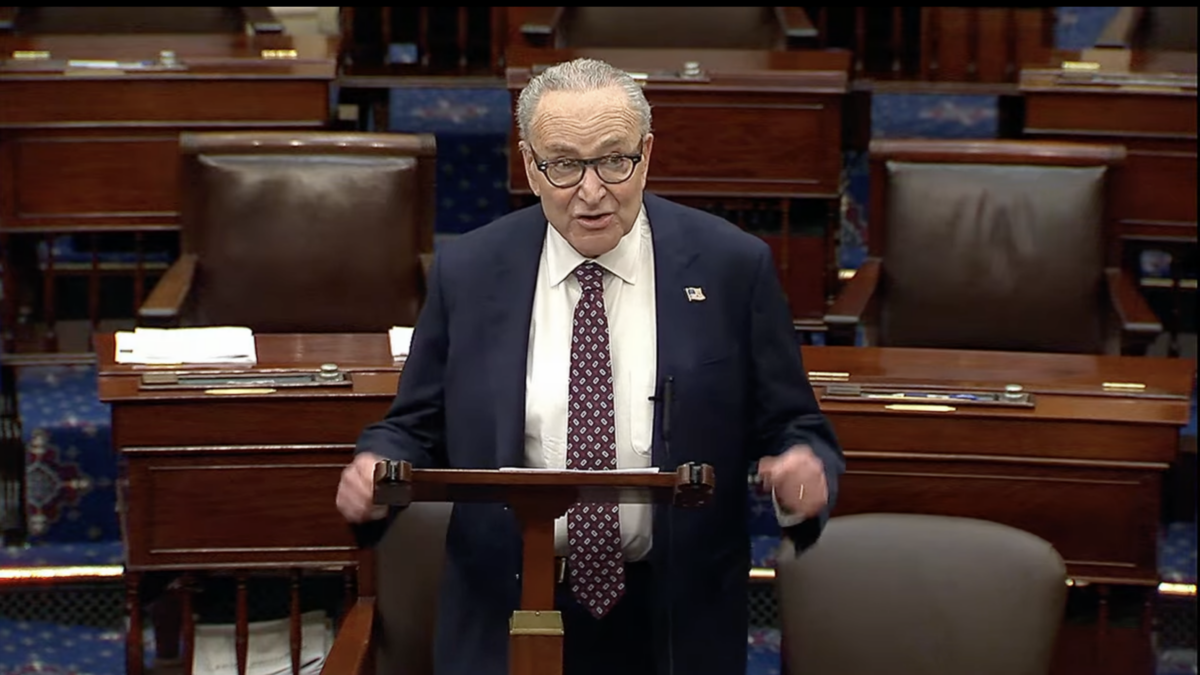
Why did Comey and the FBI agree to such an impotent, absurd, and self-defeating arrangement? Did the DNC, Hillary Clinton, or others collude with the Obama administration to prohibit such an examination? This would appear to be a fertile area for discovery by defense counsel. Depositions of Obama attorney general Loretta Lynch, FBI director Comey, and others could ask why the Obama Justice Department took no meaningful steps to properly investigate the Russia hacking narrative as alleged in the lawsuit.
What the Defense Should Investigate During Discovery
In the course of discovery, the defendants should have the DNC’s server and CrowdStrike’s work analyzed to either confirm or disprove the presence of Russian malware. If none is found, they should investigate to determine who was responsible for that deception.
Similarly, they should have the DNC files released by Guccifer 2.0 analyzed to determine if they were altered to give the false impression that the Russians had hacked the server. If so, who was responsible for the adulteration? If, as appears likely, the server was not hacked, why did Hillary Clinton and the DNC claim that it was?
Defense counsel should also investigate whether the DNC files were stolen by someone who had direct physical access to the DNC server. In that regard, who at the DNC had a motive to leak the files? Could it be someone who wanted to make public the underhanded treatment of Sanders?
Finally, since the DNC has alleged collusion by the defendants with Russia, then the Steele dossier, the very genesis of the Trump-Russia collusion story, should be open for investigation. Hillary Clinton, whose campaign funded the production of that dossier along with the DNC, would be a likely deponent, along with Glenn Simpson of FusionGPS, Steele, Sidney Blumenthal, and others who have reportedly been involved in composing the salacious and unverified contents of the dossier.
Plus, since the FBI used the dossier to obtain a warrant to spy on the Trump campaign and possibly administration, the role of the DNC, Clinton, Comey, and others in that undertaking would also be relevant to discrediting the collusion theory that underlies the DNC’s complaint.
These are but a few of the areas of inquiry that the DNC’s lawsuit has opened up to discovery. By filing its ill-conceived lawsuit, the DNC has laid itself bare to a painful and potentially disastrous discovery process that stands a better than even chance of exposing the Russia-hacking and collusion stories as carefully orchestrated falsehoods by Clinton and the DNC.
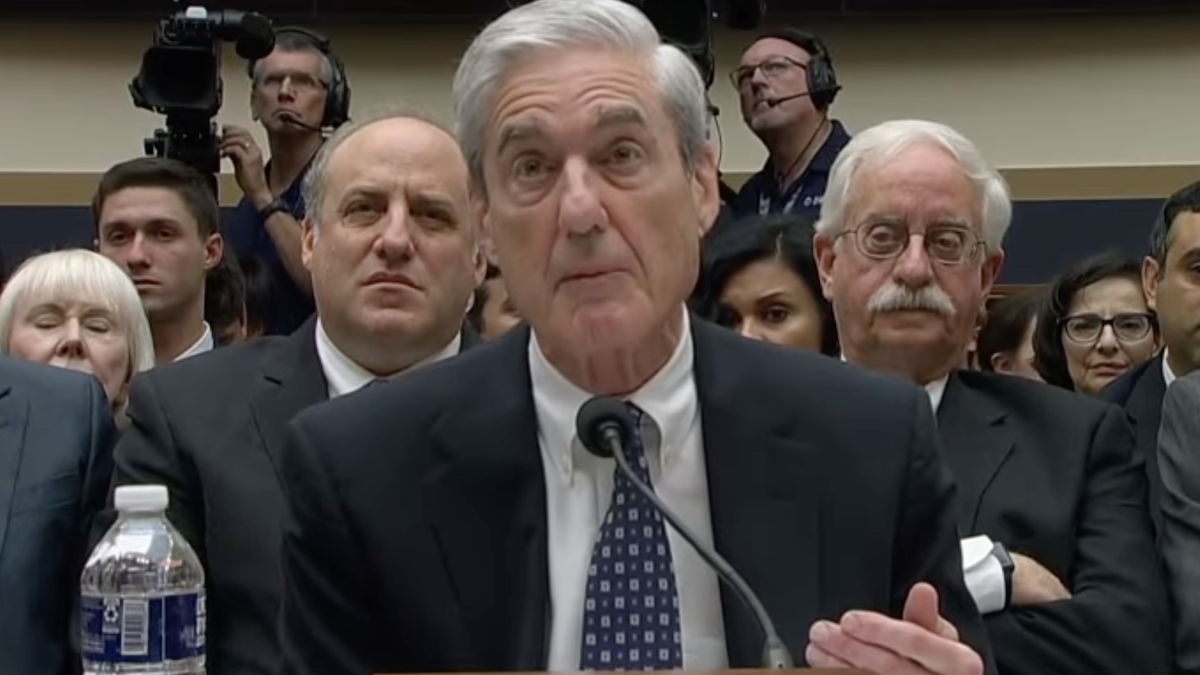
The great irony here is that the president and some of the other defendants have been calling for a special counsel investigation. Now, courtesy of the benighted DNC, they have been armed with subpoena power, the power to compel production of documents and other things, and the power to question witnesses under oath. All of these powers will be used not by a remote and secretive independent special counsel, but by lawyers working directly and solely for the benefit of the defendants.
Where will this process end? It could come to rest at Lewisburg or its equivalent. That’s the federal correctional institution where Hiss served his time.