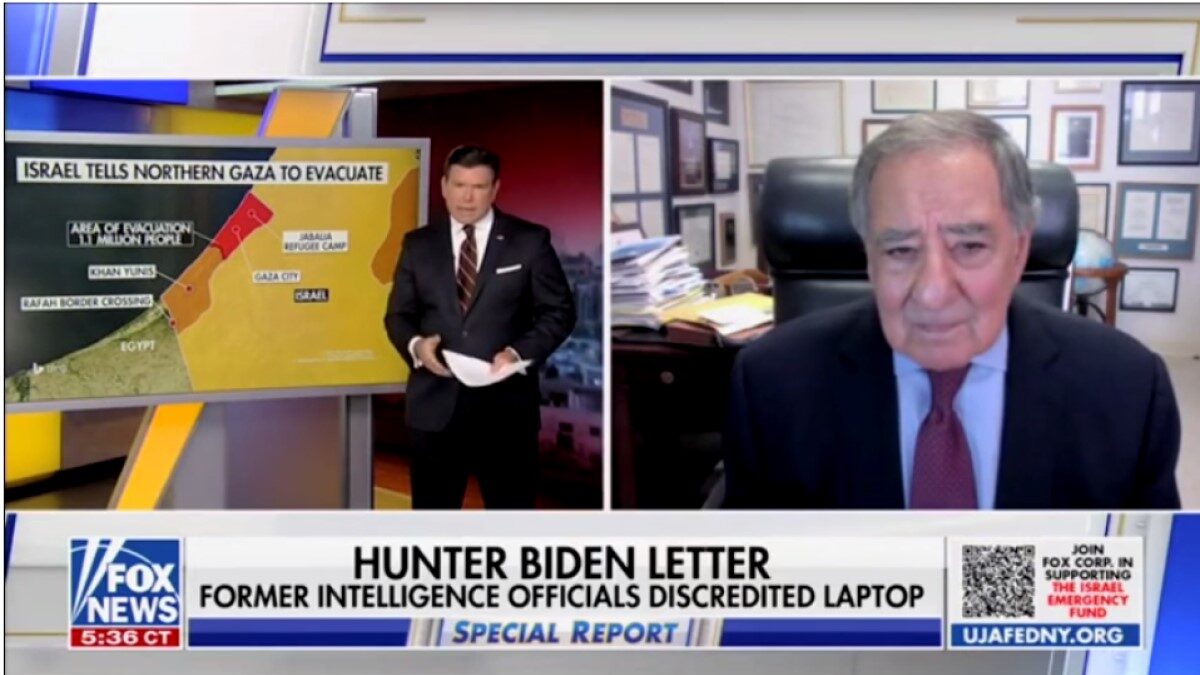
A revelation buried in a cache of documents opens a new and potentially important investigative corridor for Special Counsel John Durham. The shady tech executive who featured prominently in the federal indictment of Hillary Clinton campaign lawyer Michael Sussmann was also communicating with a covert group of computer scientists skilled in mining internet data. This revelation raises concerns that the man referred to in special counsel documents as Tech Executive-1, Rodney Joffe, may have shared sensitive government and private internet data more broadly than previously thought.
Joffe’s role in Spygate represents one of the most recent developments exposed by the Special Counsel’s office. For years, the Christopher Steele dossier stood as a headstone marking the demise of the Russia collusion hoax perpetrated on our country by the Clinton campaign and the corrupt media. But recent court filings indicate the Clinton campaign also holds blame for peddling a second con concerning the Russian Alfa Bank.
A Quick Refresher on the Alfa Bank Tale
The month before Trump and Clinton squared off in the 2016 presidential election, the media began pushing allegations that the Trump organization and the Russian-based Alfa Bank had established a secret communication channel and that the FBI had launched an investigation into that backdoor network. In indicting Sussmann, however, the special counsel’s office also revealed that the Clinton campaign bore responsibility for both the FBI probe and the press’s coverage of that fake scandal.
According to the indictment, Sussmann provided the FBI’s then-General Counsel James Baker with “white papers” and data purporting to show a secret communications channel between the Trump Organization and Alfa Bank. When he met with Baker, Sussman was representing both the Clinton campaign and Joffe, but Sussman lied to Baker about that fact, the indictment charged, telling Baker he was not working on behalf of any client.
The indictment then explained how Sussmann obtained the data and white papers showing the supposed Alfa Bank-Trump connection. According to the indictment, by July 2016, a computer researcher, now known to be April Lorenzen, “had assembled purported DNS data reflecting apparent DNS lookups between Russian Bank-1 and an email domain, ‘mail1.trump-email.com.” Lorenzen, according to Durham’s team, shared the information with Joffe and others, and Joffe told Sussmann about the data.
Joffe later “exploited his access to non-public data at multiple Internet companies to conduct opposition research concerning Trump,” according to the indictment. Joffe did this in a couple of ways, the indictment explained. First, in early August 2016, Joffe allegedly “directed and caused employees of two companies in which he had an ownership interest” “to search and analyze their holdings of public and non-public internet data for derogatory information on Trump.”
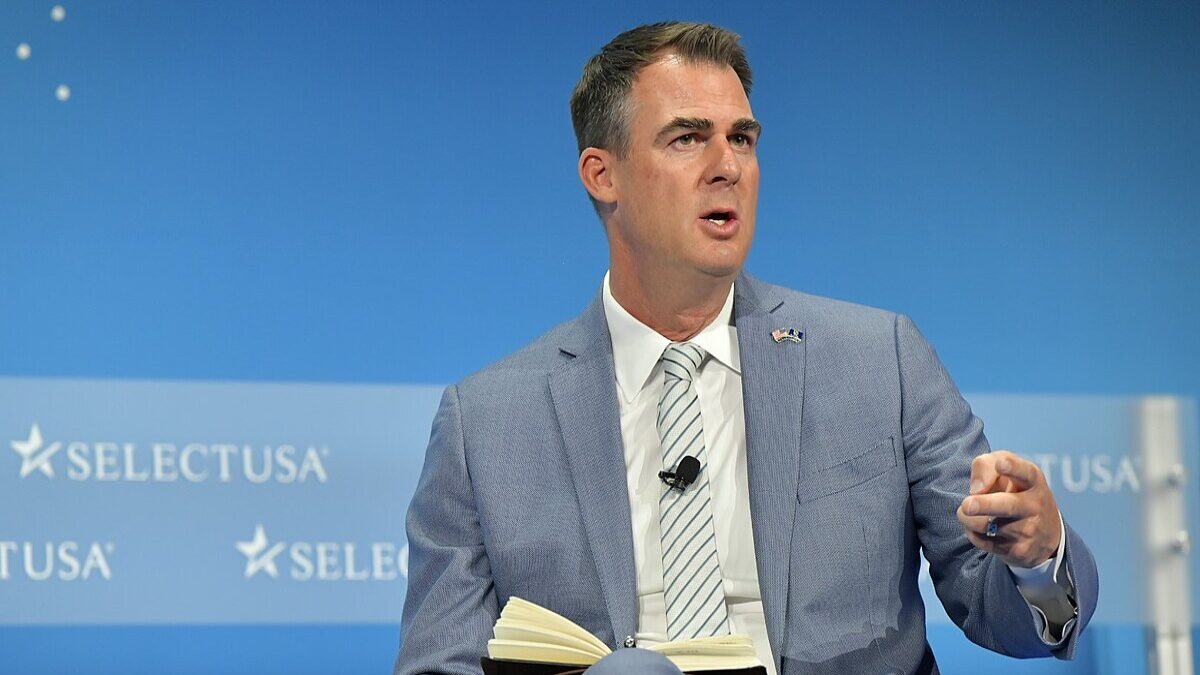
Second, the indictment claimed that Joffe enlisted the assistance of researchers at Georgia Tech, since identified as Manos Antonakakis and David Dagon. Antonakakis and Dagon, “who were receiving and analyzing Internet data in connection with a pending federal government cybersecurity research contract,” were allegedly tasked by Joffe to scour internet data “for any information about Trump’s potential ties to Russia.” Among the data Joffe provided them access to was data obtained by Joffe’s tech company in its role as a “sub-contractor in a sensitive relationship between the U.S. government and another company.”
While the indictment focused mainly on Joffe’s alleged exploitation of data to craft the Alfa Bank-Trump hoax, a subsequent filing by Durham revealed Joffe “and his associates” had also “exploited his access to non-public and/or proprietary Internet data” to track internet traffic at the Trump Tower, Donald Trump’s Central Park West apartment building, and the Executive Office of the President of the United States (EOP).
Using data culled from Joffe’s exploitation of that internet traffic, Sussmann met with the CIA on February 9, 2017, and told the intelligence service that data showed supposed connections between the Trump-related locations and the “internet protocol” or “IP addresses” of a supposedly rare Russian mobile phone provider. According to the indictment, Sussmann told the CIA that “these lookups demonstrated that Trump and/or his associates were using supposedly rare, Russian-made wireless phones in the vicinity of the White House and other locations.”
These revelations in themselves are huge, showing that, in addition to the Clinton campaign paying for the peddling of the Alfa Bank hoax, “enemies of Donald Trump surveilled the internet traffic at Trump Tower, at his New York City apartment building, and later at the executive office of the president of the United States, then fed disinformation about that traffic to intelligence agencies hoping to frame Trump as a Russia-connected stooge.”
Equally significant was the special counsel’s assertion that Joffe “exploited his access to non-public and/or proprietary Internet data,” including data Joffe’s then-internet company had come to access “as part of a sensitive arrangement whereby it provided DNS resolution services to the [Executive Office of the President].” The exploitation by Joffe of sensitive government or private data to target a political enemy should shock everyone.
But something even more explosive may be lurking beneath this scandal when the allegations contained in the Sussmann indictment are compared to the initial reporting on the Alfa Bank story.
Revisiting the Reporting
When Slate initially floated the Alfa Bank story on October 31, 2016, the liberal outlet spoke of the discovery of the supposed Alfa Bank-Trump secret communication network coming from “a small, tightly knit community of computer scientists who pursue such work—some at cybersecurity firms, some in academia, some with close ties to three-letter federal agencies. . ..”
This group, Slate stressed, had unprecedented access to internet data. “They are entrusted with something close to a complete record of all the servers of the world connecting with one another,” Slate bragged.
Then, in explaining how this community of computer scientists weaved together the Alfa Bank connection, Slate noted that Lorenzen, identified merely as “Tea Leaves” in the article, began keeping “logs of the Trump server’s DNS activity.” Lorenzen then “circulated them in periodic batches to colleagues in the cybersecurity world,” with six computer scientists in total “scrutinizing them for clues.”
The New Yorker, which revisited the Alfa Bank story in 2018 in “Was There a Connection Between a Russian Bank and the Trump Campaign,” likewise spoke of the discovery of a supposed secret communication channel as originating with “a group of prominent computer scientists” who “went on alert” after news broke of the alleged Democratic National Committee computer hack. Joffe, identified in The New Yorker article by the alias “Max,” described this small group of scientists, some of whom work “with law enforcement or for private clients,” as “self-appointed guardians of the Internet.”
According to The New Yorker’s interview of Joffe, his “group began combing the Domain Name System, a worldwide network that acts as a sort of phone book for the Internet, translating easy-to-remember domain names into I.P. addresses.” Again, The New Yorker stressed that the “group are part of a community that has unusual access to these records.”
Those searches led Joffe’s group to discover Domain Name System or D.N.S. lookups from a pair of servers owned by the Russian-based Alfa Bank. The article continued with details of the supposed strength of the evidence of an Alfa Bank-Trump network and how Joffe shared the data with his lawyer, now known to have been Sussmann. From there, the “evidence” was presented to the press and the FBI, and later to the CIA—all details included in the Sussmann indictment.
The New Yorker continued the story, moving post-election and focusing on Joffe’s continued claims of the Alfa Bank connection and efforts by Daniel Jones, a former staffer for Democrat Diane Feinstein, to “access the Alfa Bank data.”
In seeking to verify Joffe’s claims, The New Yorker reported that it also spoke with “Paul Vixie, one of the original architects of the D.N.S. network.” Vixie “affirmed that Max’s group is widely understood to have [the] capability” “to see nearly all the D.N.S. lookup on a given domain.”
Access to Secret Internet Data
Author Dexter Filkins included much more in his approximately 7,000-word tome, but it is the timing he reported, coupled with his reference to Joffe’s group of “self-appointed guardians of the Internet” that “are part of a community that has unusual access to these records” that in retrospect proves striking.
Joffe’s group reportedly claimed it scoured the internet soon after the April 2016 DNC hack, which coincides with Durham’s allegations that by July 2016, Lorenzen had assembled data purporting to show DNS lookups between Alfa Bank and the email domain, “mail1.trump-email.com,” spanning the period from May 4, 2016, through July 29, 2016.
The indictment, however, presents Lorenzen’s work as independently derived, which conflicts with Joffe’s claims to The New Yorker that after the April 2016 DNC hack, his “group began combing the Domain Name System, a worldwide network that acts as a sort of phone book for the Internet, translating easy-to-remember domain names into I.P. addresses.” Also, according to the indictment, it was not until August 2016 that Joffe allegedly began providing data to the Georgia Tech researchers to mine for information to support the inference of a Trump-Russia connection.
Where Did They Get This Access?
So where did Joffe’s group get access to the data it had reviewed? And what was the community this group was part of that has “unusual access” to the D.N.S. lookup data of “private companies, public institutions, and universities”? A random email, forwarded by Joffe to Georgia Tech’s Antonakakis, provides a possible answer: Ops-Trust.
Ops-Trust is a self-described “highly vetted community of security professionals focused on the operational robustness, integrity, and security of the Internet,” that “promotes responsible action against malicious behavior beyond just observation, analysis and research.”
According to the scant public portion of its webpage, “the community’s members, span the breadth of the industry including service providers, equipment vendors, financial institutions, mail admins, DNS admins, DNS registrars, content hosting providers, law enforcement” and other third-party security-related organizations. Membership in Ops-Trust is extremely limited with new candidates accepted only if nominated and vouched for by their peers.
While there is little public information on Ops-Trust, it is a well-known cyber-security information-sharing community, and its members appear to meet, and even make presentations at various conferences, such as the Forum of Incident Response and Security Team, or FIRST conference.
Slides still available online from a 2014 conference contain several interesting tidbits of information. First, the link to the Ops-Trust presentation includes the name “Paul Vixie,” who as noted above told The New Yorker Joffe’s group is “widely understood” to have the ability “to see nearly all the D.N.S. lookups on a given domain.”
That was not Vixie’s only connection to the story. Rather, Vixie’s name first appeared when Slate pushed the Alfa Bank tale shortly before the November 2016 presidential election. “The group of computer scientists passed the logs to Paul Vixie,” Slate wrote about the supposed discovery of the Alfa Bank-Trump connection, and then, after studying the logs, Vixie concluded that “the parties were communicating in a secretive fashion.”
The slide deck from the FIRST conference presentation also lists Vixie by name, explaining he “created the ops-t ‘portal,’” that currently boasts about “40 trust groups,” “700 members,” and an “even larger” “Crimeware” group.
Significantly, the slides also explained that “the security community now has, in Ops-T, a mature data sharing capability.” “You can stop reinventing it; join us and help out,” the slide invited. Further, every “trust group” “has its own private wiki & mailing lists,” suggesting ease of communication by this exclusive group of tech geniuses. While the Ops-Trust webpage does not display any emails, the presentation listed three with an ops-trust.net domain.
Let The Questions Begin
These details prove important for several reasons. First, the ops-trust.net domain provides a connection between Joffe and the secretive organization because in September 2018, a recent Ph.D. graduate emailed cw-general@ops-trust.net to provide his change in affiliation to the “CrimeWare” group. That email apparently went to Joffe because later that day Joffe forwarded the message to Antonakakis, asking if the sender was “one of” his.
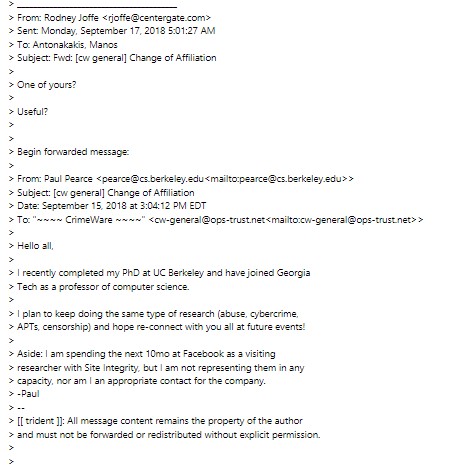
That Joffe forwarded the email to Antonakakis also suggests a connection between Antonakakis and the Ops-Trust organization.
An attempt to contact the “CrimeWare” group via the above email proved impossible, with the email coming back undeliverable. An email sent to another individual whose Ops-Trust email appeared in a separate presentation did not come back as undeliverable, but a request for comment went unanswered. And inquiries to the attorneys for Joffe, Antonakakis, Dagon, and Lorenzen were all ignored, making it impossible to ascertain whether Joffe’s group referenced in Slate and The New Yorker articles was the Ops-Trust group.
If so, an entirely new angle of inquiry emerges, with questions ranging from whether the Ops-Trust members abided by the organization’s position that they are “expected to contribute data as appropriate and in a fashion that does not violate any laws or corporate policies.”
And what about Joffe, whom Durham’s team claimed had previously pressured employees to cull company data to obtain derogatory information on Trump: Did Joffe push Ops-Trust members to assist in the Alfa Bank and Russia cell phone research?
What about the sensitive data Joffe had provided to Georgia Tech researchers: Did he also provide that data to Ops-Trust members? What about other government data Joffe or other members of Ops-Trust had access to? And what about the law enforcement members of Ops-Trust or the “three-letter federal agencies? Did any of them share in the research project targeting Trump?
These questions are not mere curiosities. Tech giants and the bloated government bureaucracy hold enormous amounts of private data and, as Ops-Trust brags, it has “a mature data sharing capability.” So what data is being shared? How is it being used? By whom? And for what purpose?
Joffe’s connection to this group and the allegations that he exploited both government and private data to target Trump mean these questions matter. So, while the special counsel’s office appears focused on the data Joffe provided to Georgia Tech, The New Yorker’s attempt to get ahead of the story of Joffe’s small band of dedicated “guardians of the internet” suggests that is where the real story lies.